Tuesday, October 31, 2006
AVG Anti Virus: Stay protected with AVG 7.5
Grisoft announced it will discontinue its free edition of AVG Antivirus 7.1. However, users can upgrade the free edition to AVG Antivirus 7.5. As some of you may know, AVG is one of the most popular free antivirus application, others include Antivir and Avast. Support for version 7.1 will end on January 15th, 2007. By the way, Grisoft's AVG Anti-Spyware application remains free for personal use as well.
Monday, October 30, 2006
RetailMeNot.com - never pay full price again with these coupon and promotion codes for online stores
RetailMeNot.com is a close cousin to BugMeNot. Unfortunately, there are websites and Internet services which require you to register with them before allowing you to use their service. BugMeNot circumvents this problem by compiling a list of user ID's and their corresponding passwords for anyone to use. The ID's and passwords are from real users who "donate" their ID's and passwords. RetailMeNot is slightly different. Instead of login information, RetailMeNot maintains a list of coupon codes for online web sites. It does not work all of the time; in fact, the success rate hovers around 20%. But 20% is better than nothing.
Saturday, October 28, 2006
Microsoft Office Validation Now Mandatory
As of October 27th, Microsoft has extended its software anti-piracy initiative to include Microsoft Office. Though the Office Genuine Advantage program started in April, it is now mandatory. Hopefully, Office Genuine Advantage program will be more accurate than the WGA validation program.
Friday, October 27, 2006
Mozilla Ships Firefox 2.0 ... It's a Dud
read more | digg story
Thursday, October 26, 2006
Make Firefox 1.5x extensions work in Firefox 2.x.
Make Firefox 1.5x extensions work in Firefox 2.x. As many of you know, Firefox 2.0 was released this Tuesday, October 24th. Unfortunately, as with previous major updates to Firefox, many of the extensions do not work in Firefox 2.0. However, it is relatively easy to edit the extension so take it can work in Firefox 2.0. Here is how to do it. First, set Windows to show file type extension. Open Windows Explorer. From the menu bar, choose Tools > Folder Options > “View” tab > scroll down to “Hide extensions for known file types” > if it is not already unchecked then uncheck it now. Now, choose an extension you want to edit. Right click it and choose “Rename.” Change the file type extension from .xpi to .zip and click [O.K.] when Windows ask if you are sure you want to change the file type. By the way, .xpi is an archival file type, much like .zip or .rar. Once you have renamed the extension, unzip the new file. You can use WinZip , a shareware, 7-Zip , a freeware, or any unzipping application. Once unzipped, there should be 2 folders and 2 files. You are going to edit the file “install.rdf.” Right click the file and choose “Rename.” This time, change the file type extension from .rdf to .txt. Use Notepad to open the newly created .txt file. There are several lines; scroll down until you see the following line:
In this case, the extension is set to work with Firefox 1.6 and older versions. Edit the line by changing the max version to 2.0. So, it should look like this:
Save the file and exit Notepad. Now, you need to do everything backwards. Change the .txt file back to .rdf file type. Next, create a new .zip file which contains the 2 folders and 2 files. Once you have the .zip file, change it back to .xpi. Now, you can install this new extension on Firefox 2.0.
Wednesday, October 25, 2006
Bypass WGA in Style
Don't have a valid copy of Windows and want to download Microsoft's free Windows software (e.g. Windows Defender). No worries, here is how to bypass the WGA validation and install Windows software. You will need to download and install Orca, which is an official Microsoft tool for modifying and validating .msi installers. Orca is part of the Microsoft Windows Server® 2003 R2 Platform SDK Web Install and can either be downloaded with the full package or as a standalone.
Final Version of Windows Defender Now Available
As many of you know, Microsoft released Windows Defender 1.1 final earlier this week. In addition, all Windows XP and Windows 2003 users will also receive 2 free calls to Windows technical support. Not bad for a freeware. However, it is not all roses over at Microsoft. There is a great deal of bickering between Microsoft and 2 security software vendors, McAfee and Symantec. In the upcoming Windows Vista operating system, Microsoft will introduce a new security feature called "PatchGuard." McAfee and Symantec want more details about the feature to optimize their software for Vista. However, until late, Microsoft has refused to provide them with details. McAfee and Symantec accused Microsoft of trying to put a strangle hold on the security software market by creating a operating system which can only support Mirosoft own software. The latter is not outside the realm of possibility since Microsoft was successful at driving out Netscape by integrating Internet Explorer to the Windows operating system.
Hacker claims to have cracked iPod, iTunes restrictions
Jon Lech Johansen (a.k.a. DVD Jon), a 22 year old Norway native who lives in San Francisco, boasts he has cracked Apple's FairPlay copy protection technology which would allow iPod to play songs purchased from music stores other than iTune. Johansen has quite a reputation in the hacker community having, at the age of 15, decrypted the copyright protection on DVD movies. He now runs a small company, DoubleTwist, based in San Francisco where he plans to license the code to businesses.
Tuesday, October 24, 2006
BetaNews | MS Adds Office 2007 to Vista Coupon Program
Great news for those people who plan to purchase a Windows based system during the holiday season. Since Microsoft Vista will not be released before the holiday season, many potential PC buyers fear that if they bought a PC now they would have to buy Vista later. So, Microsoft has developed a coupon program. The coupon would allow a person to purchase a PC now and then receive a free copy of Windows Vista when it is released. So, anyone can reap the benefits of buying a PC at holiday discount prices and not worry about spending more for a Windows OS update. Microsoft announced today that they will extend the coupon program to Microsoft Office as well. A coupon will allow people to upgrade to Microsoft Office 2007 at a substantial discounted price.
Create a Windows CD for PCs That Don't Have One
read more | digg story
Microsoft's free anti-spyware hits market | CNET News.com
Well, it's official. Microsoft has released Windows Defender 1.1 final. Windows users can now download it for free. Be aware though, to install it, you will need to go through the Windows Genuine Advantage (WGA) validation process. As some of you may remember, about 2 years ago, Microsoft acquired Giant Software Company for its anti-spyware technology. Using Giant's anti-spyware application as a template, Microsoft started developing their own anti-spyware application. During the development phase, Microsoft released a number of beta versions and refreshes. People already using Windows Defender Beta 2 will not notice any great change in the program. I am looking forward for security experts to test this final version and see how well it does or not.
Monday, October 23, 2006
Internet Explorer 7 Add-Ons
As many of you know, last week, Microsoft released Internet Explorer 7 (IE 7), a much needed update for the venerable web browser. IE 7 added many of the features already available in Mozilla's Firefox and Opera web browsers.
It seems Microsoft has also taken a page from Firefox's play book by adding its own version of extensions. One of the appeals of Firefox is the ability to add extension, which enhances and/or adds functions to the web browser. Microsoft, not to be out done, created add-ons for IE 7. Microsoft developed its own website to host IE 7 add-ons. The selection is small relative to the extensions available for Firefox but it is growing steadily. Unlike Firefox's extensions, some of the add-ons are commercial and require you to pay to use them. The website tries to make it easier for users to find what they want by dividing the add-ons in to categories, such as: security, time savers, browsers and entertainment.
Hopefully, some motivated IE users will create their own add-ons and make them available to the IE community - much like the extensions created by Firefox aficionados.
Mozilla Releases Firefox 2.0 for Windows
A day early, Mozilla releases the latest version of its popular web browser Firefox 2.0. As of this morning, Firefox 2.0 was available on Mozilla's ftp servers. For those who are already using Firefox 2.0 RC 3, there is no need to update since the final version is identical to RC 3. What will you find in Firefox 2.0? Well, version 2.0 adds built in spellchecking, antiphishing protection (i.e. developed from Google's Safe Browsing extension), search suggestions for the search box, improve tab browsing and improve javascript compliance.
Sunday, October 22, 2006
Learn How to Block Access to Selected Websites
Blocking access to websites is nothing new. For example, you can use Internet Explorer’s content advisor to block access to websites with objectionable content (e.g. pornography, gambling, etc.). But, how to block access to specific websites, not based on content, is not so straightforward. For example, how would a mother with a teenager daughter block access to MySpace? Well, one way is to edit the hosts file. I have written about Windows hosts file in the past. If you are not familiar with the hosts file then read through the article before proceeding.
How does editing the hosts file block websites? Well, Windows always searches the hosts file for a website’s IP address before searching for it on a DNS server. If you change the IP address of an URL, you essentially redirect the web browser to that assigned IP address. A computer’s IP address is 127.0.0.1 (a.k.a localhost). Whenever you change an URL’s IP address to 127.0.0.1, you redirect your web browser back to itself. In other words, it leads to a dead end.
First, create a system restore point just in case things go wrong. Next, you need to download Hoster, a free hosts file manager. Hoster does not need to be installed. Instead, just double click the .exe file and it will launch the manager. Hoster is divided in to two panels. The left panel displays the hosts file, while the controls are on the right panel. If the hosts file is marked as read-only, click [Make Hosts Writable?]. You can make a backup of the original hosts file by clicking [Create Backup Hosts File]. By default, the backup will be saved to the folder which contains the hoster.exe file. Now, you are ready to edit the hosts file. In the blank box, enter the URL of the website you want to block and click [Add to Hosts File]. For example, if you want to block MySpace then you would enter www.myspace.com (without the quotation marks). Repeat these two steps to enter additional sites to be blocked. When you are finished, just exit the program. It is that easy.
Windows Hosts File
Some of you may have heard about Windows hosts file. The hosts file is one of those things that don’t get a lot of attention. This is unfortunate since the hosts file plays a key role in internet networking.
The best way to explain the hosts file is through an analogy. Let us say you have a friend named John Doe. One day, you decided to give him a call. The first thing you need is his telephone number. You haven’t memorize his number so you go to your personal address/ telephone book – these days, it is more likely on your PDA. Unfortunately, you can’t find an entry for him. What’s the next thing you can try? You go to your 10 lbs. White Pages and look up his name. After flipping through the pages, you find his name and his telephone number. You’re going to have to learn some new terms in order to understand the hosts file. The first new word is “DNS” which stands for Domain Name System. Think of the DNS as a long list containing all the web addresses on the internet. The second word is “IP address,” which stands for Internet Protocol (IP).
Now, let’s go back to the hosts file. Each webpage has a unique URL and each URL has a corresponding IP address. For example, the URL www.yahoo.com has an IP address 68.142.226.52. You can enter either the URL or the IP address into the address bar and it will take you to Yahoo!’s homepage. Most people use the URL – it is a whole lot easier to remember www.yahoo.com than it is for IP’s 68.142.226.52. A PC’s hosts file is the “personal address/ telephone book.” And, the DNS server is the “White Pages.” When you type in a URL into the address bar and press enter, your computer will first try to find the corresponding IP address from the hosts file. If the URL is not listed in the hosts file, your computer will then communicate with a DNS server to look up the corresponding IP address.
The hosts file has its pro’s and con’s. Hackers have developed ways to edit any PC’s hosts file. First, let us talk about the bad news. Remember, the PC will first look at the hosts file before resorting to looking up an IP address on a DNS server. By editing the hosts file, hackers can redirect you to one of their sites or a porn site or use your imagination. For example, on an infected hosts file, you type www.citibank.com thinking you will be taken to Citibank’s homepage. But, instead, you are taken to a hacker’s fake Citibank homepage. The webpage look genuine and it is hard to tell the difference. When you type in your user id and password, the hackers collect that information and now have access to your bank account. There is an upside to the hosts file. You can edit your hosts file. If you know that a particular IP address leads to a malicious webpage then you can edit the hosts file to redirect the web browser to a dead end. A few good Samaritans have done the work for you. They collect URL’s that are known hacker sites. They then write up a hosts file, so when you inadvertently surf to a bad site, the hosts file redirects the web browser to a dead end.
CCleaner without the Yahoo! toolbar
read more | digg story
Saturday, October 21, 2006
What's Running on Your Computer?
Windows is always working in the background invisibly. However, once in a blue moon, you come across a process, service or program that you never noticed before and you ask yourself if this is a legitimate item or is it malware. Well, there are several free resources available on the Internet to help you to find out.
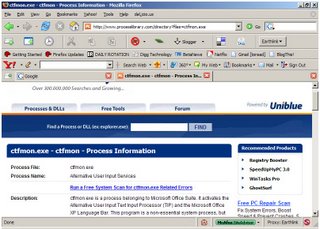
In Windows, press Ctrl+Alt+Delete to launch the task manager. Click on the “Process” tab and it will display all active processes currently running on the computer. Some of the processes are easily identifiable, such as “explorer.exe” which is for Windows Explorer. However, others are not so easy, such as “ctfmon.exe” which is for Windows language bar. On several occasions, I noticed my computer performance slowed to a crawl. I launched the task manager and discover there is a process which is hogging up 99% of my CPU. How many of you have experienced the same problem? Now, the question is should I or should I not kill the process.
 Before I do anything, I look up this mysterious process at Process Library. The website is incredible easy to use. Just enter in the process you are interested in - be sure to include the file extension as well - and then click [Search] – it’s that simple. Process Library will display the process, provide a quick summary of its function(s) and inform you if the process might be malware. There is one annoying problem with Process Library. It will display ads encouraging you to purchase their products. Just ignore it. Sorry, but there is no such thing as a free lunch.
Before I do anything, I look up this mysterious process at Process Library. The website is incredible easy to use. Just enter in the process you are interested in - be sure to include the file extension as well - and then click [Search] – it’s that simple. Process Library will display the process, provide a quick summary of its function(s) and inform you if the process might be malware. There is one annoying problem with Process Library. It will display ads encouraging you to purchase their products. Just ignore it. Sorry, but there is no such thing as a free lunch.
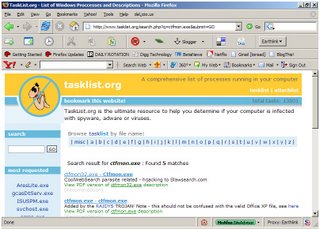 Another good alternative to Process Library is TaskList. It has comparable features. Unfortunately, it also has the same annoying problem of advertising their products. There is one feature it has and Process Library does not. TaskList also maintain a list of popular viruses found in e-mail attachments. So, if you ever receive an e-mail message from someone you don’t know, make sure to check it on this website.
Another good alternative to Process Library is TaskList. It has comparable features. Unfortunately, it also has the same annoying problem of advertising their products. There is one feature it has and Process Library does not. TaskList also maintain a list of popular viruses found in e-mail attachments. So, if you ever receive an e-mail message from someone you don’t know, make sure to check it on this website.
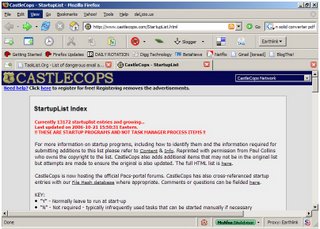
 There is one other online service I want to mention, CastleCops StartupList. Unlike Process Library and TaskList, it focuses on identifying startup programs. Castlecops maintains a list of numerous popular startup programs. Currently, the list contains 13, 172 programs and growing. Each entry is marked as either necessary or unnecessary and safe and not safe.
There is one other online service I want to mention, CastleCops StartupList. Unlike Process Library and TaskList, it focuses on identifying startup programs. Castlecops maintains a list of numerous popular startup programs. Currently, the list contains 13, 172 programs and growing. Each entry is marked as either necessary or unnecessary and safe and not safe.
Friday, October 20, 2006
Final Version of Mozilla Firefox 2 Will Be Released Oct. 24
On Wednesday, Mircosoft released it long anticipated Internet Explorer 7. As many of you know, there is a great deal of rivalry between Microsoft's IE and Mozilla's Firefox web browsers. Both organization were working very hard to have their product released before the other. In this respect, Microsoft won. However, Firefox users don't have to wait too long as Mozilla plans to release Firefox 2.0 early next week, October 24th. Unlike Internet Explorer 7, Firefox 2.0 will only add some moderate changes to the web browser, nothing earth scattering. Some new additions include: better tab browsing, integrated spell checking, anti-phishing security and suggestions from the integrated search box.
Thursday, October 19, 2006
Opera hit by security flaw - TechSpot News
Opera web browser users are urged to update to Opera 9.02. A new security flaw has been discovered in Opera which can crash the browser and even allow hackers to gain control over the computer via the browser. This security flaw affects versions 9.0 and 9.0.1. Opera version prior to 9.0 are not affected.
Microsoft: IE7 Flaw Really in Outlook Express
Some of you might have heard the rumor that Internet Explorer 7 has a critical security flaw, discovered less than 24 hours after it was released. Well, like many rumors, you should ignore this one as well. The security flaw is actually found in Outlook Express and not IE 7. Microsoft will continue to investigate the alleged IE flaw and see if there is any truth to it.
Wednesday, October 18, 2006
Microsoft releases Internet Explorer for Windows XP
Microsoft has officially released Internet Explorer 7. After months of anticipation, the popular web browser gets a major update. Internet Explorer 7 offers features long seen in other web browsers, most notably Mozilla's Firefox. IE 7 might even attract Firefox users to return to using IE. Who knows? Regardless, IE 7 is a very welcome update with many much needed security fixes.
US internet addicts 'as ill as alcoholics'
Is Internet addiction a mental disorder? A professor at Stanford University School of Medicine thinks so. Internet addiction shares the same signs and symptoms seen in other well known addictions, such as gambling or alcohol. The professor and his staff conducted an informal survey on more than 2,500 net users across the U.S.. It might be time to recognize Internet addiction as a true mental disorder which requires medical intervention.
Monday, October 16, 2006
FileForum | Mozilla Firefox 'Bon Echo' for Windows
Today, Mozilla released Firefox 2.0 RC 3. In all likelihood, this will be the last release candidate before the final version is released. Many speculate that the final version will be released sometime this month or the early part of next month. As many of you know, Microsoft plans to release its final version of Internet Explorer by the end of October. It is going to be a close race to see who comes out first. Since the fall of Netscape, Firefox has been the only real challenger to Internet Explorer's title of web browser king. If not for Firefox, it is likely Microsoft would have continued sitting on its laurel without updating Internet Explorer 6. Is Internet Explorer 7 going to be able to win back converts to Firefox?
Saturday, October 14, 2006
Saving Money How To Extend Time Limits On Free Trial Software
I love shareware which allows users to try a software program before deciding to buy it. It saddens me win the trial period ends. Fortunately, there are 2 tricks that can help to prolong the trial period. Interested?!? Read on.
Tuesday, October 10, 2006
BetaNews | Microsoft Patches 28 Security Flaws
Today, Microsoft released a total of 10 patches which fixes 28 different security flaws. However, Microsoft reports that they are experiencing problems delivering the patches. Microsoft empathized that the patches themselves are not the problem but rather the problem lies with the servers which deliver the patches.
Monday, October 09, 2006
PhishTank | Join the fight against phishing
Phish Tank allows anyone to submit a website that they think might be a phish website. All submitted suspicious sites will be investigated to determine if it is indeed a phish site. You don't need to join to reap the benefits of the project. This proves once again that you don't a big private company to create and manage a service; all you need is a community of motivated individuals who want to work together to a certain goal. In this case, the common goal is to fight scams.
Saturday, October 07, 2006
Windows Vista: Do You Want to Help Improve Windows Vista?
Microsoft has released the second release candidate for Windows Vista, Mircosoft's newest operating system. Both 32 bit and 64 bit versions are available. Testers can choose either to order a developer kit or download the .iso image file and then burn it on to a CD.
Friday, October 06, 2006
Safe and Easy Way to Boost Windows Performance (con' td)
Lets pick up from where we last left off. In my previous post, I outlined how to use Acelogix Tweak N' Tune's to boost Windows performance. I explained the tweaks on the Windows Tweak tab. Today, I will discuss the tweaks on Security Tweaks.
Security Tweak
Control Panel
- Add/Remove Program's Restrictions (All Users): the control panel is the heart of the Windows operating system. Ideally, a computer should have at least two accounts. The first account should have administrator privileges while the second is a limited account. The limited account should be used for day to day functions, such as: creating documents and checking e-mail messages. The limited account adds an additional layer of protection because it can not install or remove programs, especially important when surfing on the Internet to avoid so-called "drive-by installations." Unfortunately, this is not convenient, especially for shared computers. As an alternative, you can omit control panel applets - and thus prevent accidental installation or removal - and use multiple administer accounts. I recommend unchecking the following items:(1) Enable Add/Remove Program applet, (2) Add a program from CD or Floppy option, (3) Add programs from you network option, (4) Click here for support information hyperlink for install program.
Miscellaneous
- Prevent Accidental Batch File Execution: By default, double clicking a .bat file will execute it. Using this tweak, double clicking will only open the file for editing. This tweak is great for those of us who double click everything without thinking about it.
System
- Disable User Tracking: This is a nice tweak for those who use a shared computer.
- Make USB Memory Devices Read-Only: No one can deny the usefulness of USB memory devices, such as jump drives and external hard drives. But there is also a security risk as well. Files, saved on a hard drive, could easily be copied on to a jump drive with no one the wiser. Enable this tweak to block the download of files from the hard drive to a USB device.
BetaNews | Microsoft to Issue 11 Security Patches
Microsoft will release 11 security patches for next week's Patch Tuesday, October 1oth. 6 patches are for Windows, 4 patches for Microsoft Office and 1 patch for .NET Framework. It is suspected that there will be one or more "critical" patches.
Wednesday, October 04, 2006
Safe and Easy Way to Boost Windows Performance
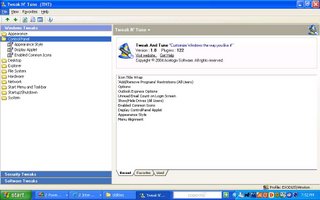 There are numerous websites which illustrate ways to optimize Windows performance. In fact, this month alone, several of these websites have been posted on Digg. As I browse through the tweaks and tips, I noticed a common element in all these Windows optimization guides. All of them included changes to Windows registry to optimize its performance. Editing Windows registry is no small matter. Even a few errors in the registry can cripple and even crash Windows. So, how can beginners and experts alike safely tweak Windows? I believe the answer is Acelogix's Tweak N' Tune utility. Let me show you why.
There are numerous websites which illustrate ways to optimize Windows performance. In fact, this month alone, several of these websites have been posted on Digg. As I browse through the tweaks and tips, I noticed a common element in all these Windows optimization guides. All of them included changes to Windows registry to optimize its performance. Editing Windows registry is no small matter. Even a few errors in the registry can cripple and even crash Windows. So, how can beginners and experts alike safely tweak Windows? I believe the answer is Acelogix's Tweak N' Tune utility. Let me show you why. Acelogix's Tweak N' Tune is freeware utility which tweaks and tunes Windows - the name pretty much says it all. With it, you can change Windows settings without having to resort to editing the registry. In addition, it will also keep a record of the changes you made, just in case you decide to restore the default settings. Let's take a look at Tweak N' Tune's main page (figure 1). There are 2 panels. The left panel lists the tweaks. The right panel has 3 tabs, which are: (1) Recent lists the tweaks that were most recently visited; (2) Favorites lists the tweaks most often visited and (3) Used lists the tweaks that were used.
Windows Tweaks:
Explorer:
- Adjust the Folder Customization Cache: Windows keeps a cache of saved folder view customizations. The cache is stored in memory; therefore, by decreasing the number of saved folders, you can free up some memory. The default size is 5,000. It can be safely decreased to a more reasonable 400. Enter "400" in the box and then press [Apply].
- Show AVI Preview in Explorer: this is a bug in the Windows operating system. When Window Explorer encounters an avi file, it will automatically start a preview of the file. Sometimes, the preview will crash Windows. It is safer to disable this feature. Uncheck the box and press [Apply].
- Thumbnails: Windows creates thumbnails (i.e. miniature representation of a image file). By decreasing the size and quality of the thumbnails, you can boost performance. Adjust the value to your liking and press [Apply]. BTW, changes in this setting only affects future thumbnails and not those which already exist.
File System:
- Avoid DLL Caching: When you exist a program, Windows still keeps some of its components in memory. Why? Because if you later decided to load the program again then it will load much faster. However, computers with less than 256 MB of RAM will benefit from unloading the cache. If you have such a computer then place a check mark for "Unload DLLs directly" and press [Apply].
- Disk Defragmenter: Windows comes with a disk defragmenter. Defragging the hard drives improves performance by placing files close together for faster retrieval. This tweak allows Windows to defrag boot files as well. Make sure the box is checked and press [Apply].
- NTFS Options: (1) Enable update of Last Access attribute. Everytime you open a file, Windows puts a time stamp on the file showing when the file was last accessed. This action slows Windows. Most users can turn off this feature and boost performance. The one exception is for backup software which requires the time stamp to synchronize files. (2) Enable 8.3 name creation. This is a compatibility feature for older software. Older 16 bit software programs (Current software are 32 bit and future software for Windows Vista will be 64 bit) use the 8.3 naming system. If your computer uses the NTFS filing system and has 16 bit software installed, Windows needs to create a file name that uses the 8.3 naming system. Most users can turn off this feature and boost performance by having Windows performing one less chore. (3) Allow extended characters in 8.3 file names. If you are disabling 8.3 name creation then you might as well disable this one as well.
- Prefetching: Windows maintains a folder of often used programs and files aptly called the "prefetch file." Prefetching allows for faster loading of programs. Make sure to select "Prefetch both (default)" and press [Apply].
Network:
- Increase Network Browsing Speed: If your computer is not part of a local area network, there is no reason to enable the search for shared printers and/or scheduled tasks. Make sure the two options are unchecked.
- Internet Time Synchronization Interval: If your computer connects to the Internet, this options allows you to adjust how frequently to synchronize your computer's time with a source on the Internet.
Start Menu and Taskbar:
- Clear Recent Documents at Shutdown: This is more of a security tweak than a performance tweak. Windows keeps a list of most recently used (MRU) documents. This tweak allows you to delete the MRU's list at shutdown.
- Menu Show Delay: When you click on a menu, there is a brief delay before the menu actually opens. You can safely decrease the delay and make menus appear faster. You can even set the delay to zero for no delay.
Startup/Shutdown:
- Allow Fast User Switching: In Windows, you can switch to another account on the computer without having to log off the current account. By disabling fast user switching, there is a slight performance boost. This is a personal preference tweak.
- AutoEnd Hung Tasks: When you log off or turnoff Windows, Windows will exit all programs which are currently active. Unfortunately, there are times when Windows fails to exit a program. When this happens, Windows displays a dialog box prompting the user to manually force the program to exit. Save yourself the trouble and enable this feature to end automatically without any prompting.
- Clear Page File: Oftentimes, a computer has insufficient RAM installed. Windows solves the problem by converting a portion of the hard drive to act as virtual memory. The virtual memory has many names, like paging file or swap file. Clearing the paging file during shutdown will greatly increase the time it takes Windows to close. The only good reason to clear the paging file is for security. The paging file contain programs and data which is readily accessible.
System:
- Crash Control > Error Reporting: When an error causes Windows to crash, on the next reboot, Windows will prompt you to send an error report to Microsoft. Microsoft uses the information to improve their products. Microsoft promises that no personal information is included in the report but why take the risk. You're better of just disabling error reporting.
- Memory Settings: (1) Use large system cache. If you are using a workstation(e.g. personal computer) then you are better off not using this tweak. Windows by default allocates more memory for opening and using programs. Using a large system cache is better suited for servers. (2) Force the core Windows system to be kept in memory. Earlier, I mentioned that there are two types of memory which Windows users, RAM and virtual memory. RAM is considerable faster than virtual memory. This tweak keeps the core Windows system files in RAM instead of pushing it to virtual memory, which greatly increase Windows performance. I recommend enabling this feature for all users.
This is part 1 of the series to improve Windows performance. We will pick up tomorrow where we left off today.
BetaNews | Microsoft to Lock Pirates Out of Vista
In its efforts to stem software piracy, Microsoft has added a number of security features to Windows Vista which would cripple the operating system until it has been validated. Some examples include: disabling the Aero user interface, disabling ReadyBoost, disabling Windows Defender and a watermark on the desktop. Many Windows users have reported problems with the Windows Genuine Advantage (WGA) program. Experts believe as high as 42% of copies of Windows deemed not genuine by WGA were in fact geniune. Hopefully, the program for Windows Vista will not suffer the same problem.
Tuesday, October 03, 2006
Firefox Zero-Day Code Execution Hoax?
Here is an update to the story about 2 presenters at ToorCon Converntion claiming Firefox has over 30 vulnerabilities centered around its javascript controls. The 2 presenters, Mischa Spiegelmock and Andrew Wbeelsoi, have since retracted their statements. Spiegelmock, in particular, claims that his statements were meant to humor people. In fact, to the best of his knowledge, the vulnerabilities he reported would only crash the browser and not allow execution of random code. Mozilla's engineers continue to investigate the vulnerabilities reported. Personally, I think both of them owe Mozilla and the Firefox community a very big apology. If you want to tell a joke, tell it to your with friends at a social gathering and not at a professional conference.
Exclusive: Here Comes Windows Vista RC2
Rumors are spreading throughout the cyberworld that Microsoft plans to release Windows Vista RC 2 on Friday. This will be the last pre-release before the final version. However, Microsoft has the uncanny ability to delay the release of any of their products. Well, we have to wait and see.
Monday, October 02, 2006
Free Security Applications for Windows
Let me be clear here, there is no shortage of good free security software programs. Therefore, there is no good reason for anyone not to have at least an antivirus and firewall installed on their PC. While viruses are still the number one threat to business and home PC's, adware and spyware are growing at a tremendous rate. Gone are the days in which an introverted computer hacker starved for attention takes to digital world and creates a virus for boasting rights. Now, malware is driven by money. Be it a botnet that launches a denial of service attack or phishing scam which steals your user ID and password, it is grief that you do not need. As the old proverb says "a pinch of caution is better than a pound of trouble." Below, I have gathered a not so short list of security freewares. Where possible, I listed if a download requires registration. In addition, I provided links to reviews for the software. You can find the reviews at the bottom of the article. Enjoy!
Antivirus Scanners
- Antivir Personal Edition Classics free for home and non-commercial use. Antivir has very good detection and removal rates. It comes with heuristic scanning for zero day exploits. One weakness is that it does not scan incoming e-mail messages. However, it can scan outgoing e-mail. When updating new virus signatures, it will display a splash screen for their premium products, which is a little annoying. In addition, it takes it takes a while to download the new signatures. No registration required. (1)
- AOL Active Virus Shield a free version of Kaspersky Lab Antivirus. Kaspersky Lab is one of the most respected security software vendor. Prior to Active Virus Shield, Kaspersky Lab only offered commercial products. AOL has negotiated with Kaspersky Labs to produce a lite version of its popular antivirus. AOL Active Shield was released shortly after AOL's debacle of releasing the search data of more than 650,000 users. Perhaps, this is their way of redeeming themselves. This lite version has one of the best detection and removal rates. Registration required. (2)
- Avast Home Edition free for home and non-commercial use. Avast was one of the very first free antivirus. It has a decent detection and removal rates. Unlike Antivir, it will scan incoming and outgoing e-mail messages. The most recent version includes intrusion detection functionality. Basically, it monitors key areas in Windows operating system and alerts users if it detects something trying to change these areas. Registration required every 4 months. (1)
- AVG Free Edition free for home and non-commercial use. Again, AVG is one of the very first free antivirus for personal use. Its detection rate is subpar. But, long time users swear by it as the best free antivirus available. Grisoft, the parent company which owns AVG, has recently acquired Ewido Anti-Spyware (Ewido is mentioned later in this article) Despite its name Ewido Anti-Spyware provides protection from spyware and Trojan horses. It is very likely that Grisoft will include Ewido's technology in to future version of AVG. AVG is a small program and requires little computer resources, which makes it a good choice for older computers. No registration required. (1)
- Comodo Antivirus free for all users. Comodo Antivirus is one of the newer entrants to security software industry. It boasts very good detection and removal rates. Comodo has been criticize for including adware in their products but this should be taken with a grain of salt. Registration required.
- Computer Associates Antivirus free for all users. Computer Associates is the maker of the popular anti-spyware PestPatrol and Etrust antivirus. This free version comes with a 12 month subscription of virus signature updates. It detection and removal rate is subpar. It is a small program and requires little computer resources, which makes it a good choice for older computers. Registration required.
Firewalls
- Ashampoo Firewall free for all users. Shampoo is one of the newer entrants in to the security software industry. Their firewall is very easy to use and requires very little resources, which makes it a good choice for older computers. It is a work in progress and users can expect to be a few bugs but that is true about all the other firewalls in this article. Registration required.
- Comodo Firewall free for all users. Comodo is one of the new entrant to the security software industry. PC Magazine has given rave reviews for Comodo Firewall and PC Magazine rarely gives any software such a high rating. Proving once again, free is not synonymous with poor quality software. Registration required. (3)
- Outpost Firewall Free free for home and non-commercial use. Outpost Firewall is small but efficient. One unique feature it has is the ability to add plugin to extend its functionality. For example, it has a plugin to remove banner ads. Registration required. (4)
- Sunbelt-Kerio Firewall comes with a 30 day trial. After trial period some advanced functions disabled. Almost a year ago, Kerio made the decision to stop developing their home firewall products and focus instead on their firewall products for businesses. Fortunately, Sunbelt (makers of the popular anti-spyware CounterSpy) stepped in and took over the development of Kerio Personal Firewall and changed the name to Sunbelt-Kerio Firewall. Kerio is one of the best firewalls I ever used. It has two modes; one mode is for novices and the other is for advance users. Free for all users. No registration required (4)
- Sygate Personal Firewall free for all users. Sygate is truly a great firewall but, unfortunately, it is no longer being developed. People can still download the last free version but be warn there is no support for this product. No registration required. (4)
- ZoneAlarm Free for home and non-commercial users. ZoneAlarm is almost a household name. ZoneAlarm Firewall is included in ZoneAlarm Internet Security Suite. However, they do provide a lite version of their famous firewall. In the beginning, ZoneAlarm will prompt the user to either permit or deny connections but, once trained, the number of prompts drops tremendously. Registration required. (4)
Adware and Spyware Scanners
- Lavasoft's Ad Aware Personal free for home and non-commercial use. The free version is identical to the commercial version except it does not offer any real time protection. The controls are a little confusing and sometimes you need to dig deep in to subfolders to find the settings you want. Nevertheless, it has decent detection and removal rates. No registration required. (5)
- Spybot Search & Destroy free for all users. Spybot is one of the first anti-spyware application ever made - if not the first one. It offers real time protection. Though I would recommend you not turn on the "Tea Timer" real time protection feature. It is more suited for Internet Explorer than any other web browser. It adds a large list of malicious websites to IE restricted zone. In addition, users can add Spybot's hosts file. Spybot can lock the hosts file, IE's homepage and IE's default search engine. No registration required. (5)
- Windows Defender (beta 2) free for all Windows users. To download Windows Defender, you need to have already gone through the Windows Genuine Advantage (WGA) validation process. A few years back, Microsoft acquired Giant Software, an anti-spyware software vendor, and used their technology to create Microsoft Anti-Spyware. Later, Microsoft changed the name to Windows Defender. Windows Defender is still in beta testing. Personally, I think Microsoft took a very good piece of software and butchered it. However, it does offer better real time protection than the other two anti-spyware applications. Windows Defender will be included in Windows Vista, Microsoft's newest operating system.
Trojan Scanners
- A squared Free free for all users. The free version does not have any real time protection. You need to purchase the commercial version to add real time protection. No registration required.
- Ewido Anti-Spyware comes with a 30 day trial period. After trial period, real time protection is disabled but all other features are still enabled. Don't be fooled by the name, Ewido is one of the best - if not the best - Trojan horse detector and remover.
Rootkit Scanners
- BitDefender Anti-rootkit Uncover beta is free during the beta testing period. Requires registration to become a beta tester. Bitdefender plans to add Uncover to its future Internet Security suite.
- F-Secure Blacklight beta is free during the beta testing period. Blacklight is the fastest of the scanners. F-secure plans to add Blacklight to its next Internet Security suite. No registration required.
- Sophos Anti-rootkit is free all users. No registration required. Sophos plans to continue providing a free version of its rootkit remover. I haven't had time to test Sophos Anti-Rootkit but have read some very good reviews.
- SysInternal Rootkit Revealer is free for all users. It is the slowest of the free rootkit scanners. Its a very good scanner but it generates a report which is hard for non experts to understand.
Anti-Phish Toolbars
- Cloudmark Anti Fraud Toolbar is only available for Internet Explorer
- Earthlink Scam Blocker Toolbar is available for both Internet Explorer and Firefox.
- Netcraft Anti-Phishing Toolbar is available for both Internet Explorer and Firefox.
- Windows Live Toolbar is only available for Internet Explorer. Windows Live Toolbar comes with a anti-phishing module. The same module will be included in Mircosoft's newest Internet Explorer 7.
Reviews
(1) "Review: Free Antivirus Software" -- written by Mary Landesman,about.com. (http://antivirus.about.com/od/antivirussoftwarerev)
(2) "AOL Active Virus Shield" -- written by Robert Vamosi, cnet.com. (http://reviews.cnet.com/AOL_Active_Virus_Shield/45)
(3) " Comodo Firewall Review" -- written by Neil J. Rubenking, pcmag.com. (http://www.pcmag.com/article2/0,1759,1969207,00.as)
(4) "Firewall Reviews" -- written by Neil J. Rubenking, pcmag.com. (http://www.pcmag.com/article2/0,1895,1864603,00.as)
(5) "Spyware Fighter" -- written by Narasu Rebbapragada, pcworld.com(http://www.pcworld.com/article/id,126818/article.h)
Sunday, October 01, 2006
Download Messages From Yahoo! Mail For Free
As many of you know, the free version of Yahoo! Mail does not provide POP3 access. In layman's terms, you can't download messages from Yahoo! Mail to your desktop e-mail client. In order to receive POP3 access you need to upgrade to Yahoo! Mail Plus, which will cost you $19.99/ year. However, there is a poor man's alternative to gain POP3 access to Yahoo! Mail and it won't cost you a dime.
YPOP is a free open source application which allows users to access their messages from Yahoo! Mail. Currently, it supports the following OS: Windows, Mac, Solaris and Linux. It supports several popular desktop e-mail clients, such as: Outlook, Outlook Express, Thunderbird and Eudora. Use of YPOP's in no way violates your license agreement with Yahoo! Mail. How does it work? Here is what the developers' had to say:
""How do we do it you ask? Well, this application is more like a gateway. It provides a POP3 server interface at one end to talk to email clients and an HTTP client (browser) interface at the other which allows it to talk to Yahoo!"
You can download YPOPs at SourceForge.net. For instructions on how to install and configure it for your desktop e-mail client, see the following links:
- Outlook (Windows XP)
- Outlook 2003
- Outlook Express
- Mozilla Thunderbird
- Eudora
For the complete list of desktop clients supported, go to Email Clients.
YPOPs developers provide YPOPs for free but welcome any donation to continue developing YPOPs.
Hackers claim zero-day flaw in Firefox | CNET News.com
Two presenters at the Toorcon Hacker Conference revealed a JavaScript exploit in Mozilla's Firefox web browser. Mozilla's chief of security was not too please with discoverers revealing the hack code for the flaw instead of quietly bringing it to the attention of Mozilla. The flaw will be hard to patch since it affects a root portion of the code. Users can install the NoScript extension as a temporary solution.